Here are shown some examples of devices that have differing degrees of two parameters:
However,
the fundamental issue that separates the underlying philosophy
of wearable computing from that of ubiquitous
computing is not really the fact that it is wearable
(the Wearability/Portability axis), but, rather the fundamental
difference in the two philosophies is best captured by the
Existentiality axis
(Mann 1998, Proc. IEEE)
See the following discussion figure:
Here are shown some examples of devices that have differing degrees
of two parameters:
The answer, of course, is in the existentiality axis, not the portability (wearability) axis. By bringing our own camera, we have much greater control of the picture taking process. For example, we can take a picture and own the copyright, whereas if we rely on pictures taken by others, they own the copyright in our image, even though it might be a picture of us. The real issue here is control of information, not the degree to which the apparatus is portable or wearable. However, there is an important relationship between the two axes, because if we wear (or carry) the camera, we control the data from it, but if we rely on an organization's cameras, they control the data.
Indeed, we could, as a society, take all the money we spend on our own cameras, and spend this money instead on public cameras owned by the government. If we did this, we could have our dream of cameras and microphones and computers everywhere come true, and we would never need to carry or wear our own, because there would be so many of them in the environment. However, it is the author's opinion that this would not turn out to be the utopian world we would want to live in. Indeed, it has been the author's experience that the more cameras that are installed in the environment, the less likely we are to be permitted to have our own. Establishments like gambling casinos, department stores, and government buildings with surveillance cameras often try to watch for, and prevent persons from using their own cameras to take their own pictures.
Thus the fundamental issue explored in this paper is the Existentiality axis, and its relation to the Wearability/Portability axis.
What was learned from the wide range of experiences attained in inventing, designing, building, and actually wearing these machines, in a wide variety of ordinary day--to--day settings (e.g. not just in a lab), was that there are two fundamental classes of problems, quite apart from the technical feat of getting the machines to actually work. These classes of problems are (1) the effect, often undesirable, the apparatus has on the wearer in long term use, as well as (2) the effects the apparatus has on other people. The first will be called ``first--person detriment'', whereas the second will be called ``second--person detriment''.
Although there are many facets to each of these two classes of problems, such as:
This strong reaction (2) goes beyond merely a mild social stigma or avoidance leading to lonliness, but also includes, in the author's personal experience:
Accordingly, the author identifies the two fundamental axes of the Reality Mediator (RM) in day--to--day life:
These more fundamental philosophical aspects are the far more important ones, especially in view of the fact that the author has invented, designed, and built systems that are completely covert and relatively comfortable to wear, and that these systems are clearly easy to manufacture. Therefore, the cumbersome and burdensome aspects of the apparatus, as well as the social stigma associated with looking strange, are moot points, once we can mass produce comfortable and covert embodiments.
It is the author's view that a Reality Mediator is of most benefit when it is worn over a long period of time, so that, as a computational framework, it leads to a constancy of user--interface. In order for there to be widespread acceptance of this apparatus, it may well need to have the appearance of ordinary eyewear (e.g. be covert).
There are two classes of experimental subjects, the long term subject (the author), and external subjects, primarily officials, authority figures, and the like. The long term subject (the author) represents, admittedly, a small sample size of one person, but given the length of the experiment (more than twenty years), new and insightful results were obtained. It would be unreasonable, at this point, to have a large sample population wear these devices for a twenty or thirty year time period. Thus results based on the long term subject (the author), fall under an experimental paradigm related to that of George Sratton's experiments published in 1896 and 1897 in Psychology Review, in which the experimental subject was himself.
More recently Gibson (Gibson 1972) formalized this ecological approach to the study of perception in general, in which he emphasized using available environmental information in visual perception studies. The ecological approach differs from the conventional approach to psychology in this sense of external versus internal experimental validity.
The operation of the depth tracking
aremac is shown in the Figure:
CAPTION: Focus tracking aremac:
(a) with a NEARBY SUBJECT, a point P0
that would otherwise be imaged at P3 in the EYE of a user
of the device is instead imaged
to point P1 on the image SENSOR, because the
DIVERTER diverts EYEward bound light to lens L1.
When subject matter is nearby, the L1 FOCUSER moves
objective lens L1
out away from the SENSOR automatically,
as an automatic focus camera would. A signal from
the L1 FOCUSER
directs the L2 FOCUSER, by way of the FOCUS CONTROLLER,
to move lens L2 outward away from the light SYNTHesizer.
At the same time, an image from the
SENSOR is directed through an image PROCessor, into the
light SYNTHesizer. Point P2 of the display element is
responsive to point P1 of the SENSOR. Likewise other points
on the light SYNTHesizer are each responsive to corresponding
points on the SENSOR, so that the SYNTHesizer produces a complete
image for viewing through lens L2 by the EYE, after reflection
off of the back side of the DIVERTER.
The position of L2 is such that the EYE's own lens L3
will focus to the same distance as it would have focused in
the absence of the entire device.
(b) With DISTANT SUBJECT MATTER, rays of parallel light
are diverted toward the SENSOR where lens L1 automatically
retracts to focus these rays at point P1. When lens L1
retracts, so does lens L2, and
the light SYNTHesizer ends up generating parallel rays of light
that bounce off the backside of the DIVERTER. These parallel
rays of light enter the EYE and cause its own lens L3 to relax
to infinity,
as it would have in the absence of the entire
device.
Because the eye's own lens L3 experiences what it would have experienced in the absence of the apparatus, the apparatus, in effect, taps into and out of the eye, causing the eye to become both the camera and the viewfinder (display). Therefore the device is called an Eye Tap device.
In stereo versions of the proposed device, there are two cameras or measurement systems and two aremacs that each regenerate the respective outputs of the camera or measurement systems.
The apparatus is usually concealed in dark sunglasses
that obstruct vision except for what the apparatus allows to pass through.
Because the experimental apparatus is built to be used in ordinary
day--to--day life, and not the lab, it must have an appearance of
ordinary eyewear and ordinary clothing, so that the test subjects
do not seem to regard it as an unusual apparatus.
The experimental apparatus is shown in the Figure:

CAPTION: The author's wearable computer system (as pictured on the
cover of Toronto Computes, 1999) consists of a small computer that fits
in a shirt pocket, and apparatus concealed under ordinary clothing.
The eyeglasses, which provide an infinite depth of focus
image, have a normal (e.g. not an unusual) appearance.
However, another aspect of the experiment is to explore, in an experimental fashion, the second person detriment.
In order to do this, the author built a variety of systems in which the overtness (degree of obviousness that a camera was present) could be varied.
The goal of this work was to set forth an hypothesis that the overtness is actually a function of the other variables, and to understand the relationships between these variables.
The test subjects were chosen from among those who appeared to show the greatest anger toward the author from earlier years of wearing the less covert (more cumbersome) variations of the apparatus. It was found previously that those persons who are part of an organization extensively using video surveillance were more likely to complain when the author had a personal safety device. Most notably, it was the representatives of surveillance regimes who most notably complained about being held accountable. Thus the experimental subjects were drawn from:
A ranking scale, based on the immediate reaction of the subject to being photographed, or imaged with video apparatus, was used as follows:
It is hypothesized that the overtness axis may be considered to be an independent variable, in the context of the ranking scale listed above. In particular, to reduce the dimensionality of the problem, isoscore lines (lines of constant score) passing through a multidimensional space, provide overtness as a function of other independent variables.
In this way, overtness was varied as an independent variable, while noting the effect of other concomitant variables, while noting what level of overtness as a function of one point would provide the same score as another level of overtness for another point, and so on.
This approach answered the the fundamental question as to which of the following functions of overntess and score were most important, and how they were related:
The following Figure illustrates an individual interacting with a clerk
who either is, or pretends to be, under the control of a manager who either
is, or pretends to be under the control of a chief technology officer,
who either is, or pretends to be, under the control of a board of directors,
etc..:
This figure is a diagram depicting an INDIVIDUAL versus a CLERK.
The CLERK is bound by, or pretends to be bound by, conditions from
a MANAGER. For example, the CLERK may be protected by a
surveillance camera, or may be protected by a conspicously covert
container for a surveillance camera (such as a large plexiglass hemispherical
dome of wine dark opacity). Alternatively, the CLERK may be
protected by a blatentized covert surveillance potential,
such as a blatently displayed television connected to a hidden camera.
If the INDIVIDUAL complains about the surveillance, or about the potential
for surveillance (e.g. by asking about plexiglass hemispherical
domes of wine dark opacity within the establishment), the CLERK
can either claim to not know what's in the domes, or can absolve himself
or herself from responsibility for the situation by making reference to
the MANAGER. The CLERK can either claim that the MANAGER
installed the surveillance cameras, or authorized or required the installation
of the cameras, or that
the MANAGER decides whether or not images are captured from these domes.
Alternatively the CLERK can completely deny knowing whether or not the domes
actually contain cameras.
Similarly, the MANAGER is bound by, or can pretend to be bound by conditions from a chief technology officer (CEO). The CE0 is bound by, or pretends to be bound by what the insurance company requires, or by a board of directors, denoted BOARD.
A typical example of such a situation is when a person tries to negotiate with a used car salesman, and the used car salesman might say something like ``I'd love to give you the car for one thousand dollars; let me check with my manager''. The used car salesman then disappears into a back room, has a coffee, and reads a newspaper for a few minutes, and then comes out and says ``I'd love to give you the car for one thousand dollars by my manager won't let me.''. Although the salesman never talked to a manager, the salesman has some degree of power over the customer by virtue of being able to credibly pretend that he is bound by a higher authority. A credible, articulable, higher and unquestionable authority allows representatives of organizations to obtain external blame and excuses for their otherwise irrational or disagreeable actions.
Unfortunately the individual person does not ordinarily enjoy the same luxury as the clerk, and must therefore behave more rationally, or risk seeming irrational, rude, or otherwise inappropriate. For example, if an individual carried a handheld video camera around videotaping clerks, casino operators, police officers, customs officials, and the like, the individual might be regarded as strange, rude, or otherwise acting in an inappropriate manner.
The individual could rely on religion, as a manager, by, for example, wearing a camera contraption as part of a religious order. Just as religion allows individuals to wrap their heads in various materials that would otherwise be regarded as inappropriate, a new religion such as the ``personal safety religion'' could be invented, that required its members to wear cameras.
Thus religion could form a similar purpose to the manager for the individual, but there is the danger that others (including clerks) may dismiss the individual as a religious freak. Therefore, what is needed is a similar way for the invididual to have excuses for and to externalize blame for otherwise irrational or disagreeable actions.
An important aspect of the invention is for the individual to be able to nonconfrontationally inflict fear of accountability, uncertainty, or doubt on persons exerting physical or other coercive force, or the threat or possibility thereof, upon the user of the invention. This can be done by way of an incidentalist imaging possibility.
Incidentalist imaging refers to imaging which can be made to seem as if it occurs merely by chance or without intention or calculation. An incidentalist imaging system may in fact blatantly capture images (as by an articulable requirement from a higher authority to do so), or it may present itself as a device that could capture images in a way in which it is difficult to discern the intentionality of the use of the invention.
The following Figure illustrates an individual who either is, or pretends to be,
under the control of a Safety Management Organization (SMO).:
This figure shows an embodiment of the WearComp invention in which
the INDIVIDUAL
has a credible mechanism to externalize at least a portion of his or
her image capture actions to a Safety Management Organization (SMO).
The SMO provides an
articulable basis upon which to deny free will or self determination.
The SMO creates a management system, either real or percieved by others,
that forces the CLERK out of the normal role, making necessary a
true back channel (REVERSE PATH) from the CLERK to the MANAGER, which will
often also require a true back channel to the CEO, etc..
Ordinarily there would be no such back channel, or the back channel would be reduced. For example, if an INDIVIDUAL complains about video surveillance systems in use by a CLERK, then the CLERK will simply refer the INDIVIDUAL to management, and management will be likely only available on certain limited hours, and after waiting extensively and being held up and delayed in line extensively. Then management will likely say the directive for use of surveillance comes from head office, and refer the INDIVIDUAL to a head office, where the INDIVIDUAL will spend several hours waiting on hold and calling various telephone numbers, etc.. The head office will then often say that the surveillance is used because the insurance company requires it.
However, if the INDIVIDUAL takes out his or her own personal handheld camera and photographs the CLERK, indicating that the SMO requires it, a very fast back channel (REVERSE PATH) will arise. Quite often the MANAGER will immediately become available, and the INDIVIDUAL will no longer have to wait in line or come back on a certain special day to talk to the manager. The matter will rapidly escalate to the highest available level of authority.
This system has a symmetrizing effect in which the individual and manager either snap out of their respective roles, or a back channel is forced, disrupting the normally one--way nature of the control flow from the top--down of management to the CLERK. Thus the individual human becoming a clerk forces the clerk to become an individual human and make responsible decisions outside the scope of just being a clerk.
In addition to an SMO, the INDIVIDUAL can also choose to be bound by (or to pretend to be bound by) an SMO that is itself bound by a higher authority such as an insurance company. Thus, in one embodiment, the INDIVIDUAL could, for example, take out a life insurance policy that required him to wear a personal safety device that recorded video at all times.
Thus an individual wishing to wear a video capture and recording system merely signs up with a life insurance company that requires him to do so. A small premium of one cent per year could be paid by the individual primarily for the reason of being bound by the requirement to wear the device. For example, the life insurance company could provide the individual with a choice of two programs, one being one cent a year wearing a camera, and the other being two cents a year not wearing the camera. Thus the individual wishing to wear a camera system simply selects the lower premium, and then blames his apparently irrational actions (like constantly wearing a camera system) on the insurance company.
Thus the life insurance company has provided the individual with a means for articulably externaizing his own irrational actions. Now the individual can say ``I'm wearing this camera because my manager (SMO) requires it, and the insurance company requires the SMO to require me to wear it, etc.. This reverse chain of command is denoted by amplifier 104B.
Preferably, in the experimental apparatus, a PROCEDULARIZER is used to allow the individual to follow, or to appear to follow, a prescribed procedure without appearing to be thinking for himself or herself. The lack of apparent individual thought or intentionality, allows the individual to become or seem to become a clerk, which is what forces the CLERK to be human in being forced to think and make decisions for himself or herself.
Moreover, a secret input (SELF DEMOTION) to the amplifier may actually originate by the INDIVIDUAL. In this sense, the INDIVIDUAL is actually bound by his own wishes. Thus the SMO may actually be directed by the INDIVIDUAL to bind the INDIVIDUAL to certain terms and conditions.
In the case of the physical system, the binding may be legal or actual, in the sense that individual receives or appears to receive an electrical corrective signal (e.g. electric shock) for not complying with the requirements of the SMO.
An example of such a system includes a system or method of doing business for an individual wishing to have a right to connectivity to communications infrastructure. The individual could choose to receive a shock for each packet of data lost. Therefore a clerk or official trying to force the individual into a room or space with poor wireless connectivity would thus be giving the individual painful electric shocks. In this way, a clerk or official trying to force the individual into a basement elevator, holding room, or the like, would be committing an act of torture. In this embodiment, the system provides the individual with the right to have other persons at remote sites monitor how he is being treated.
That which falls upon the EXISTENTIALITY axis is thus at the core of this paper, and central to its theme. Thus it is important to understand both the subtlety of this axis, as well as some of the extreme points on this axis.
To explore some of the extremes of this axis, the author has built a number of experimental setups which take this axis to its extremes. The reader should understand, of course, that these are not meant as normal operating points in this space, but, rather, are meant to define end points where one would not normally operate or use in the manufacture of a commercial embodiment of the invention.
Other similar constructs involved creating T shirts that were part of
a company uniform, that the author was required to wear, when running
errands on company time. Thus the author would be required to wear
a personal safety device, and then enter establishments where
video was prohibited. Examples of the shirts appear
in http://wearcam.org/maybecam.htm
as shown in the Figure:

Additionally, just as department stores have television screens
hanging from the ceiling as a reminder of video surveillance, so
also can the individual.
http://wearcam.org/sicherheitsglaeser/, as shown in the Figure:
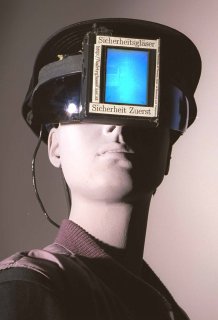
In the author's Plenary Symposium session
at Ars Electronica, entitled "Sicherheitsglaeser: Sicherheit Zuerst" in 1998,
these qualatitive finding that the use of the wearable computer for denial
of existentiality (and denial of selectivity) allows the individual person
to become a clerk and force clerks to become human was presented.
Later in one of the talks, Mark Weiser presented his views on
Ubiquitous Computing.
At this time, the two views were quite distinct, but are obviously
related.
Here, even though the camera is completely hidden in the eyeglasses, the VGA television screen from a body worn computer displays a view from the camera on a WWW browser running on the body worn computer, so that when someone looks at the wearer they see themselves on a WWW page by way of the covert Web camera. This level of overtness is even more powerful and visceral than that of the Ubiquitous Surveillance television screens hanging from the ceiling in department stores because people ordinarily pay a great deal of attention to eye contact with the individual, but when the subjects try to make eye contact with the wearer of the apparatus, they see instead a reflection of themselves. Thus this apparatus is called ``mirrorshades'' because the Web mirror site is an actual reflection image of the person as if they were looking at themselves in a mirror, which is also mirrored at various other WWW sites.
These eyeglasses are nonselective in the sense that everyone encountering the wearer is a photographic subject.
The degree of overt nonselectivity is also adjusted on an ambigous axis,
by using domes, so that the devices borrow from the iconography of the
gambling casinos and department stores, but re-situate these symbols
in the everyday prosthetic territory of the individual,
as shown in
http://wearcam.org/domes
as in the Figure:


These domes were varied in size, and varied in placement on the body.
Additionally, the amount of extra apparatus was varied. In some
experiments, a large transmitting antenna was used, and a control
panel to the Terminal Node Controller (TNC) was displayed so that clerks
and other officials could see the blinking lights of the data transmission
process. In other experiments, only the dome was shown, and everything
else was hidden.
2. for a given overtness, acceptability and each of the three independent axes vary in roughly the shape of a rectangular hyperbola.
3. for a given level of overtness and acceptability, any two of the three independent axes vary approximately in the shape of a rectangular hyperbola.
Dr. Mann has been inventing, designing, and building wearable computers for more than 20 years, dating back to his high school days in the 1970s. He brought his inventions and ideas to the Massachusetts Institute of Technology in 1991, initiating, what was to later become the MIT Wearable Computing Project. He also built the world's first covert fully functional WearComp with display and camera concealed in ordinary eyeglasses in 1995, for the creation of his award winning documentary ShootingBack. He received his PhD degree from MIT in 1997 in the new field he had initiated. He is also the inventor of the wristwatch videophone, of the chirplet transform (a new mathematical framework for signal processing), and of the comparametric image processor.
Mann proposed the first IEEE International Symposium on Wearable Computing (ISWC97), and was also Publications Chair of that conference.
He also chaired the first Special Issue on Wearable Computing to appear in an academic journal (Personal Technologies Journal), and has been the keynote speaker at numerous scientific and industry symposia and conferences. He has also been an invited speaker at numerous university Distinguished Lecture Series and colloquia. His work has been featured in leading international fora for the general public, such as The New York Times, LA-Times, Time, Newsweek, Fortune, WiReD, NBC, ABC, CNN, David Letterman Top Ten, CBC-TV, Scientific American, Scientific American Frontiers, Discovery Channel, Byte, Reuters, New Scientist, Rolling Stone, and BBC.